
Employee Monitoring & Insider Threat Detection — Managed by ITECS
Gain real-time visibility into user activity, detect insider threats before they escalate, and generate audit-ready compliance evidence with Teramind — fully deployed and managed by ITECS.
The challenge
The insider threats your security stack can't see
Firewalls and endpoint protection stop outside attackers — but they're blind to the risks that start inside your organization. Without employee activity monitoring, data walks out the door unnoticed.
of breaches involve a human element
Undetected data exfiltration
Employees copy sensitive files to personal cloud storage, USB drives, and personal email daily. Without user activity monitoring, data exfiltration goes unnoticed until it becomes a reportable breach.
average cost of an insider-driven breach
Compliance audit failures
HIPAA, PCI DSS, and SOX auditors require continuous activity logs and tamper-resistant evidence. Without employee monitoring, proving compliance is guesswork — and failed audits carry six-figure penalties.
average time to contain an insider incident
Slow incident investigation
Without behavioral baselines, investigating insider threats takes weeks of manual forensics. Real-time alerts and session recordings cut investigation time from days to minutes.
Teramind managed by ITECS
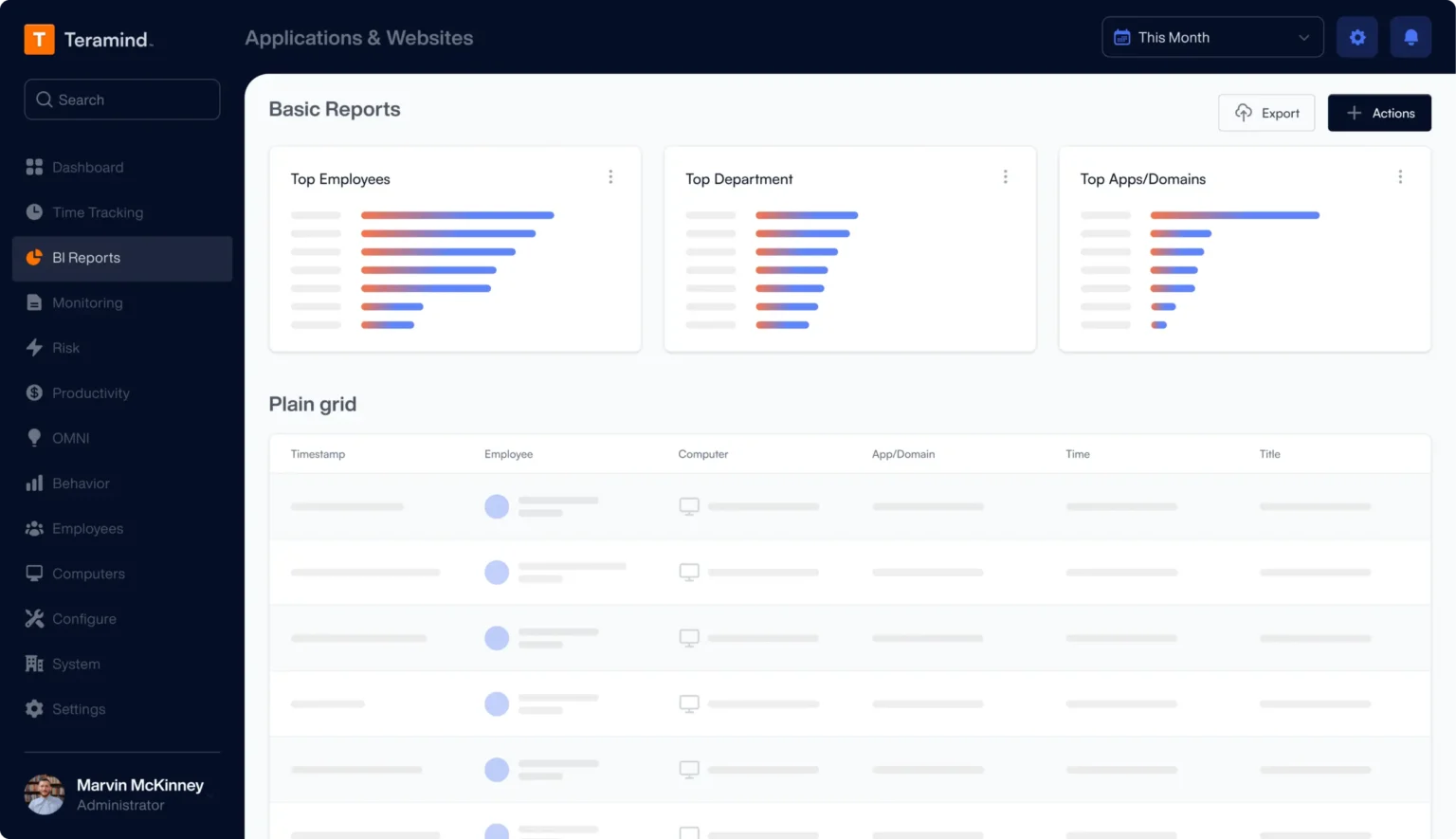
Employee monitoring, insider risk detection, and DLP — in one platform
Teramind gives your security team real-time visibility into user activity across every endpoint, application, and communication channel. Combined with behavioral analytics and data loss prevention, it closes the insider threat gap that traditional security tools miss.
- Monitor employee activity across apps, email, web, and file transfers
- Detect anomalous behavior and enforce DLP policies automatically
- Generate audit-ready compliance reports for HIPAA, PCI DSS, and SOX
- ITECS handles deployment, policy design, tuning, and ongoing oversight
Explore how monitoring integrates with our cybersecurity services, or see deployment options for virtual desktop and RDP terminal server environments.
Outcomes
Four pillars of employee monitoring protection
Teramind delivers measurable security, compliance, and productivity outcomes — all managed by ITECS.
Behavioral Data Loss Prevention
Detect and block risky data movement across USB, cloud storage, email, and printing — before sensitive files leave your network.
Prevent data exfiltration in real time
Continuous Compliance Monitoring
Automatically capture audit-ready activity logs, screen recordings, and regulatory reports that satisfy HIPAA, PCI DSS, SOX, and GDPR auditors.
Stay audit-ready year-round
Workforce Productivity Analytics
Measure active vs. idle time, top applications, and workflow patterns so managers can make data-driven decisions about team efficiency.
Turn activity data into actionable insights
Insider Threat Detection & Response
Combine anomaly detection, dynamic risk scoring, and automated interventions to identify and contain insider threats before they escalate.
Reduce investigation time from days to minutes
Compare monitoring tiers
Teramind Starter vs. UAM vs. DLP — which tier fits your business?
Each Teramind license tier builds on the previous one, adding deeper monitoring capabilities and compliance controls. ITECS recommends the right fit based on your industry, data sensitivity, and regulatory requirements.
| Feature | Starter $15 per user per month | UAM $30 per user per month | DLPMost complete $35 per user per month |
|---|---|---|---|
| Activity Monitoring | |||
| Screen Recording & Live View | |||
| Website & App Monitoring | |||
| Instant Messaging | |||
| Email Monitoring | |||
| File Transfer Monitoring | |||
| Keystroke Logging | |||
| Printing Activity | |||
| Clipboard Monitoring | |||
| Behavior Analytics | |||
| Insider Threat Detection | |||
| Productivity Analysis | |||
| Anomaly Detection | |||
| Dynamic Risk Scoring | |||
| Data Loss Prevention | |||
| Content-Based Rules | |||
| Exfiltration Prevention | |||
| Data Fingerprinting & Tagging | |||
| Regulatory Compliance Tools | |||
| Audit & Forensics | |||
| Video Session Recording | |||
| Full-Text Search | |||
| OCR Content Search | |||
| Smart Rule Templates | |||
Not sure which tier is right for your organization? ITECS evaluates your compliance requirements, data sensitivity, and monitoring objectives to recommend the optimal fit.
Prices shown are Teramind MSRP. Terminal server licensing also available below.
Core monitoring capabilities
User activity monitoring that drives action
Behavior baselines + anomaly detection
Profile normal user activity and flag deviations that indicate insider risk or policy violations.
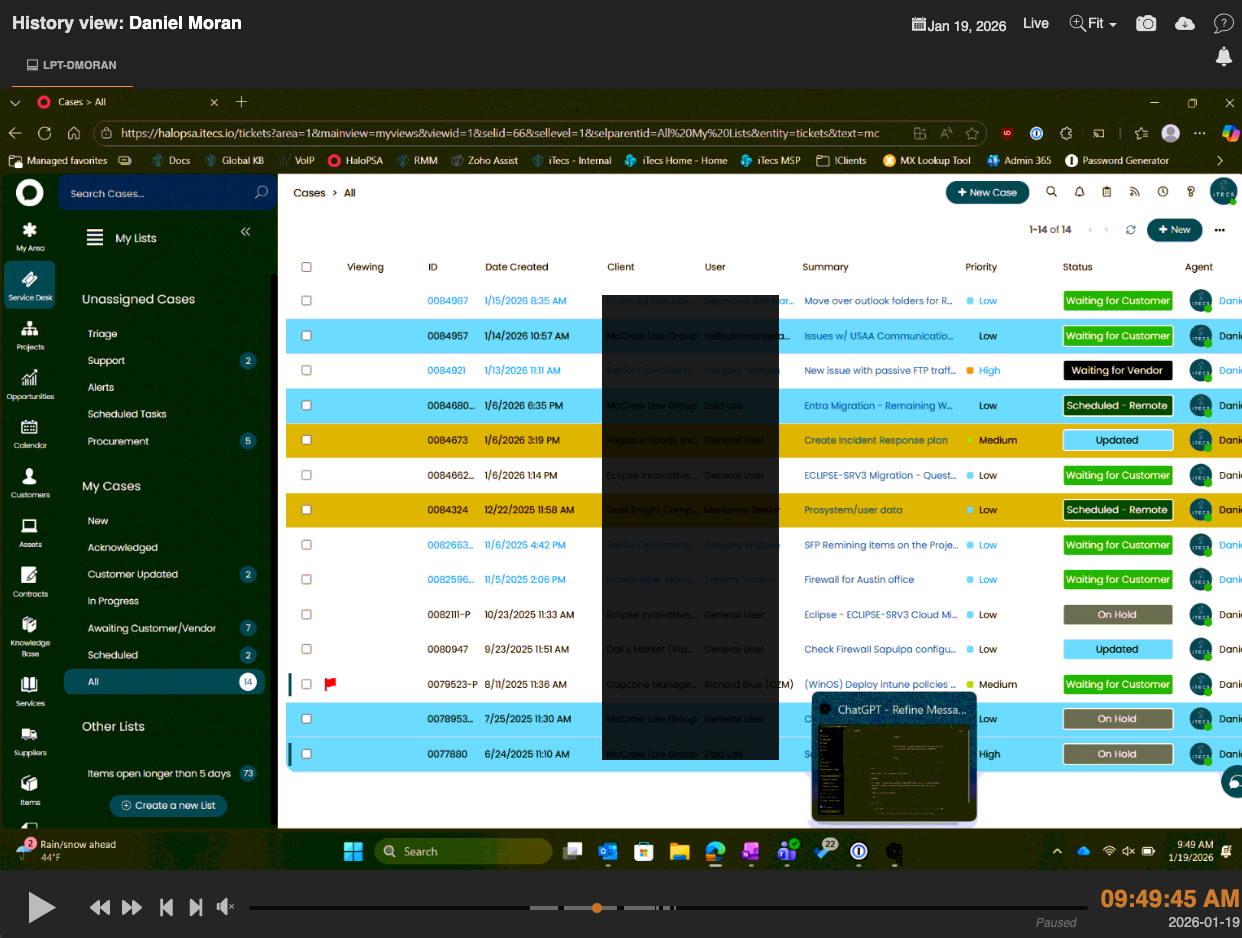
Screen recording + session playback
Record endpoint sessions and replay the exact moments surrounding an incident for rapid forensic review.
Multi-channel activity monitoring
Capture user activity across applications, web, email, file transfers, and messaging from one unified console.
OCR + content inspection
Detect sensitive data inside screenshots, screen shares, and images to close DLP blind spots.
Real-time intervention controls
Automatically notify, block, or terminate sessions when monitoring policies are breached.
Role-based access + policy rules
Apply least-privilege monitoring tailored by role, department, or risk level.
OMNI AI alert intelligence
Prioritize insider threat alerts with AI-powered risk scoring and news-feed style insights.
SIEM/SOAR integrations
Send Teramind events into Sentinel, Splunk, or any SIEM/SOAR for unified security operations.
Live screen monitoring
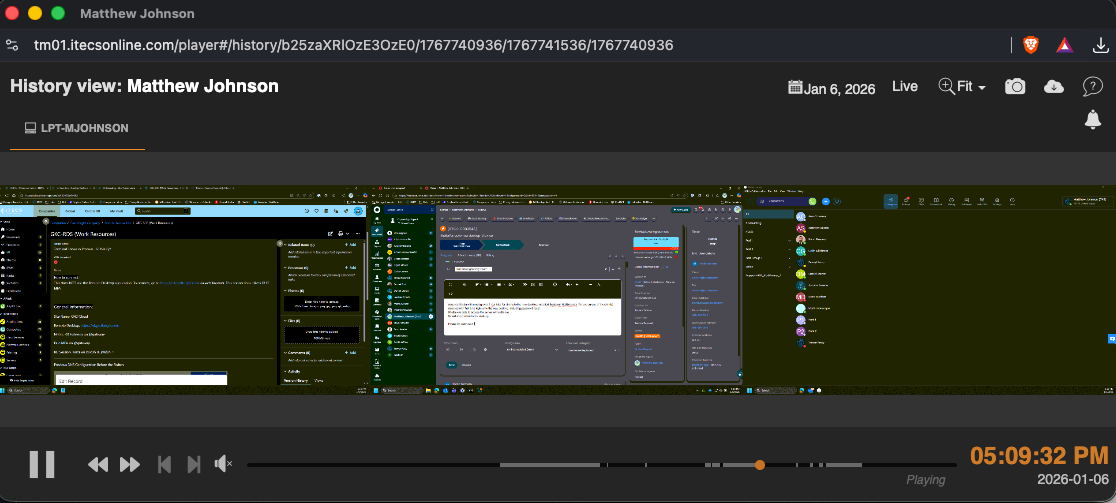
Watch one screen or monitor the entire floor in real time
Teramind Viewer: multi-monitor oversight
Watch one or many employee screens simultaneously with Teramind Viewer. Switch between live sessions, replay historical screen recordings, and zoom into specific user activity to investigate insider threats or verify policy compliance in seconds.
Comprehensive behavior analysis
Deep visibility into every channel
These capabilities power the behavior insights, investigations, and policy automation teams rely on.
OMNI: AI-powered alert feed
Surface the most important alerts first with a prioritized, news-style feed that accelerates investigations.
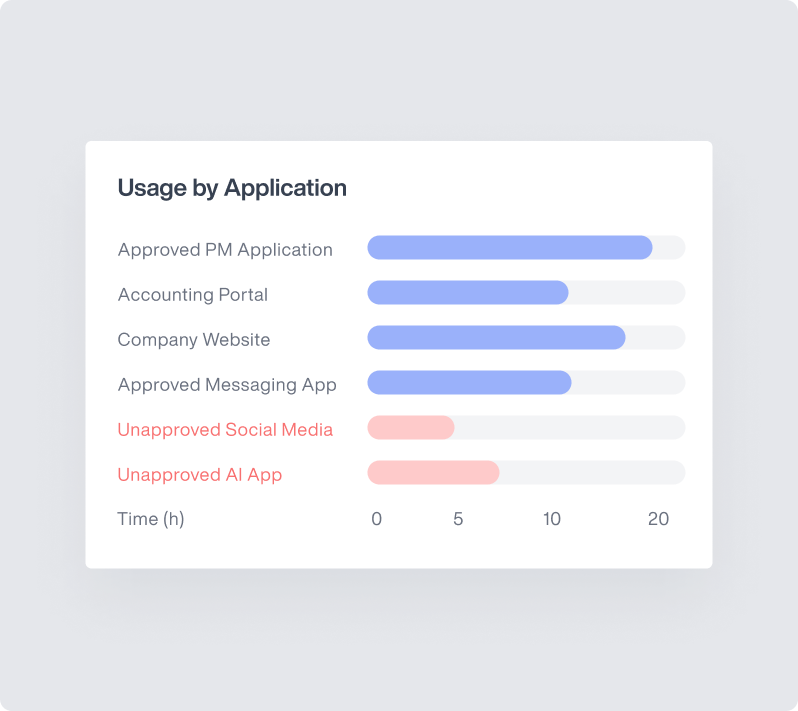
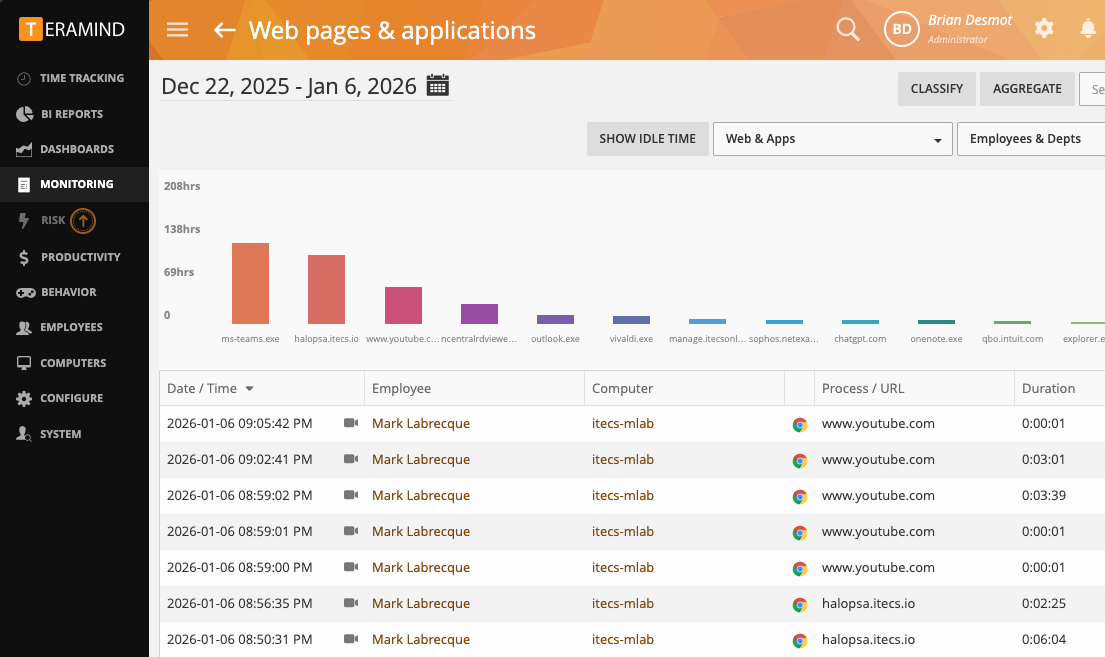
Website & application monitoring
Track how web apps and internal tools are used, and enforce who can access them and how they are used.

Instant messaging monitoring
Analyze chat behavior to understand collaboration patterns and detect messaging that violates policy.

Time-stamped screen recordings
Replay the exact moments around an incident to establish context and speed investigations.
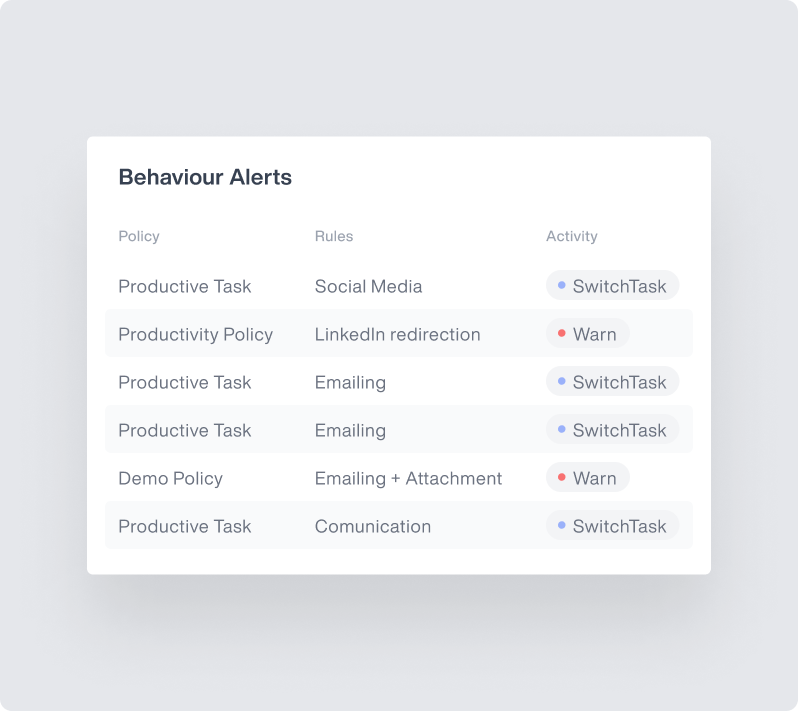
Smart rules & automated responses
Trigger alerts or auto-enforce controls for high-risk actions like sensitive uploads, downloads, and printing.
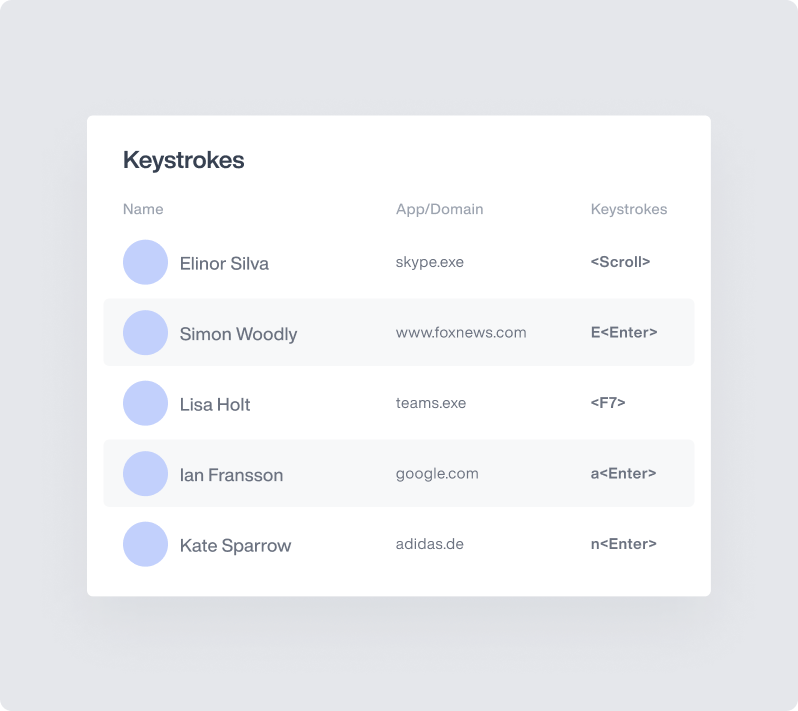
Keystroke logging
Capture searchable keystroke data to support investigations and policy enforcement.
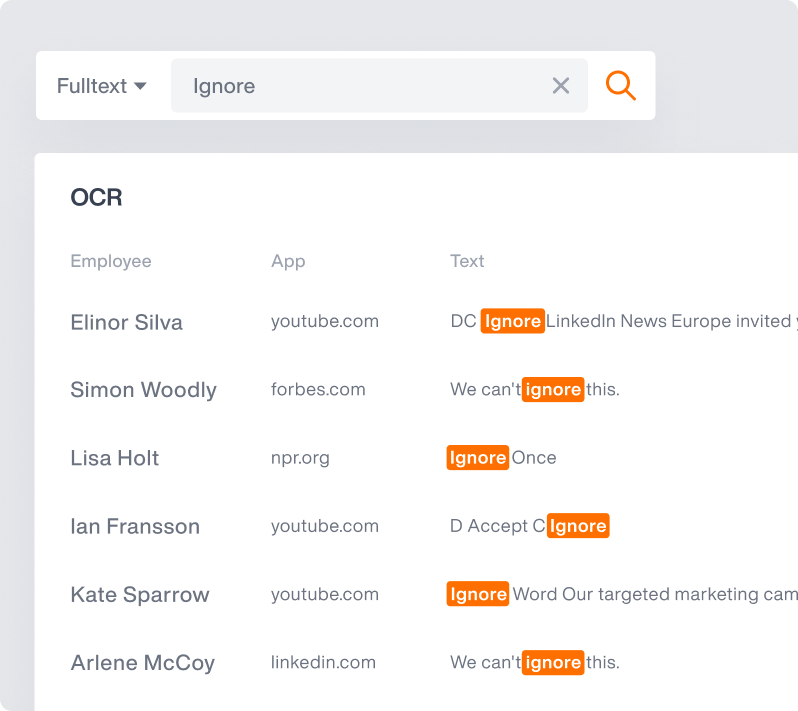
Optical character recognition (OCR)
Detect sensitive text inside screenshots and screen shares to close DLP gaps.
Industry-specific monitoring
Employee monitoring tailored to your industry's compliance requirements
Healthcare, financial services, legal, and manufacturing organizations face unique insider risks and regulatory mandates. ITECS maps the right Teramind tier to your specific compliance and data protection needs.
Healthcare
DLP recommendedHIPAA compliance requires content-level monitoring and PHI exfiltration prevention.
Key threats addressed
- PHI exposure
- EHR misuse
- Unauthorized data sharing
Financial Services
DLP recommendedPCI DSS and SOX require audit trails, data classification, and exfiltration controls.
Key threats addressed
- Client data theft
- Fraud patterns
- Trading violations
Legal
DLP recommendedClient confidentiality and attorney-client privilege demand content-aware DLP.
Key threats addressed
- Privilege leaks
- Document exfiltration
- Unauthorized case access
Manufacturing
UAM recommendedInsider threat detection and productivity monitoring protect IP and optimize output.
Key threats addressed
- IP theft
- Production sabotage
- Productivity loss
Why choose managed monitoring
Self-managed Teramind vs. ITECS-managed monitoring
Teramind is a powerful employee monitoring platform — but extracting real security and compliance value requires dedicated expertise. ITECS bridges the gap between software and outcome so your team can focus on acting on insights, not managing the tool.
| Capability | Self-managed | ITECS-managed |
|---|---|---|
| Monitoring policy design | Your team researches best practices from scratch | ITECS designs monitoring policies aligned to your compliance framework and risk profile |
| Agent deployment | Internal IT installs, configures, and troubleshoots | Fully managed rollout across all endpoints, terminal servers, and VDI environments |
| Alert tuning | Constant noise leads to alert fatigue and missed threats | ITECS tunes thresholds for high-signal, low-noise insider threat detection |
| Executive reporting | Manual report creation when leadership asks | Monthly executive reports with risk trends delivered on schedule |
| Incident escalation | No defined workflow — ad-hoc responses | Documented escalation playbooks with defined SLAs and incident response procedures |
| Platform maintenance | Your team tracks releases and manages upgrades | ITECS manages all updates, patches, and configuration changes with zero disruption |
Deployment timeline
From policy design to production monitoring in 4–6 weeks
Every ITECS-managed Teramind deployment follows a proven four-phase process that minimizes disruption and accelerates time to value.
Discovery & policy design
ITECS conducts a monitoring needs assessment, maps your compliance requirements, and designs employee monitoring policies aligned to privacy and risk objectives.
Monitoring policy document + deployment plan
Agent deployment & configuration
Teramind agents are installed and configured across all endpoints, terminal servers, and VDI environments — with zero disruption to daily operations.
All endpoints reporting to Teramind console
Alert tuning & team training
Alert thresholds are refined to eliminate noise, your security team is trained on dashboards and investigation workflows, and monitoring coverage is validated.
Tuned alert rules + trained security team
Ongoing managed oversight
ITECS delivers monthly executive reports, triages insider threat alerts, adjusts monitoring policies as your environment evolves, and manages escalation workflows.
Monthly reports + continuous policy optimization
Teramind pricing
Transparent employee monitoring pricing — endpoint and terminal server options
Choose per-endpoint licensing for distributed teams or per-server licensing for shared RDP and VDI environments. ITECS evaluates your user density and compliance needs to recommend the most cost-effective licensing model.
Endpoint licensing
Per user / month — ideal for distributed and hybrid teams
Starter
Basic screen recording and productivity tracking
$15.00
/ user / mo
UAM
Full activity monitoring with behavior analytics
$30.00
/ user / mo
DLP
Complete DLP with compliance and data protection
$35.00
/ user / mo
Terminal server licensing
Per server / month — cost-effective for 30+ users per server
Starter
Basic monitoring for all users on terminal server
$450.00
/ server / mo
UAM
Full activity monitoring for all users on terminal server
$900.00
/ server / mo
DLP
Complete DLP for all users on terminal server
$1050.00
/ server / mo
Prices shown are Teramind MSRP. ITECS managed-service fees are quoted separately based on scope. Request a custom quote.
Regulatory compliance monitoring
Audit-ready compliance evidence for regulated industries
Teramind generates the continuous activity logs, screen recordings, and tamper-resistant audit trails that compliance auditors require. ITECS aligns your monitoring policies, DLP controls, and reporting cadence to the specific regulatory frameworks your organization must satisfy.
Supported compliance frameworks include:
Explore related services
Need the bigger picture? Start here.
This page covers one area of cybersecurity. If you want to compare all of our security services, see how they fit into managed IT, or get a risk assessment, these pages have you covered.
All cybersecurity services
Compare endpoint protection, firewall management, email security, consulting, training, and compliance options.
Compare cybersecurity options
Cybersecurity overview
See the full ITECS managed security approach — 24/7 SOC, layered defense, and MSSP positioning.
View cybersecurity overview
Managed IT services
See how cybersecurity integrates with managed IT support, cloud, and strategic planning under one partner.
See managed IT plans
Case studies and white papers
Review real outcomes that support security planning, executive buy-in, and budget justification.
See case studies
Cybersecurity assessment
Get a prioritized view of your risk exposure, control gaps, and recommended next actions.
Run the assessment
Our Partners










Employee Monitoring & Insider Risk FAQ
Common questions about Teramind deployment, compliance monitoring, and ITECS managed services from Dallas businesses.
Teramind captures user activity across apps, websites, files, messaging, and screen sessions. It combines behavioral analytics with policy enforcement to improve productivity, reduce risk, and create audit-ready evidence.
Teramind creates tamper-resistant activity logs, screen recordings, and reporting templates that support HIPAA, PCI DSS, SOX, GDPR, and other frameworks. Higher license tiers unlock deeper DLP and compliance tooling.
Yes. ITECS designs a privacy-aligned monitoring policy and can deploy visible or limited monitoring modes based on role, department, and regulatory needs.
Starter focuses on core visibility and productivity tracking. UAM adds behavior analytics, anomaly detection, and deeper activity monitoring including email, keystrokes, and file transfers. DLP adds content inspection, clipboard monitoring, data fingerprinting, and compliance controls for regulated industries.
Endpoint licensing is priced per user. Terminal server licensing is priced per server and covers all users connecting to that shared environment, which can be more cost-effective in RDS, Citrix, or VDI deployments with 30 or more users per server.
Yes. Teramind agents are deployed to individual endpoints regardless of location. ITECS handles configuration, policy deployment, and ongoing monitoring for office, remote, and hybrid workforces.
Teramind supports cloud (SaaS), on-premise, and private cloud deployments. ITECS recommends the best option based on your data residency requirements, security posture, and existing infrastructure.
A typical ITECS-managed deployment takes 4 to 6 weeks from policy design through production rollout. This includes discovery, agent deployment, alert tuning, and team training.
ITECS brings 23 years of security operations expertise to every Teramind deployment. We handle policy design, rollout, alert tuning, monthly reporting, and escalation workflows so your team can focus on acting on insights rather than managing the platform.
Get your free Teramind monitoring assessment
Tell us about your insider risk concerns and compliance requirements — ITECS will recommend the right Teramind tier, deployment strategy, and monitoring policy design for your organization.
Customized monitoring policy recommendations aligned to HIPAA, PCI DSS, SOX, or CMMC
Deployment plan optimized for your endpoint, VDI, or terminal server environment
Alert tuning strategy to eliminate noise and surface real insider threats
ITECS-managed oversight with monthly reporting and escalation workflows
Free Teramind Assessment
Teramind Monitoring Assessment
Typical response within 1 business day
Ready to close your insider threat visibility gap?
ITECS deploys and manages Teramind so your team gets insider risk detection, compliance evidence, and workforce analytics — without the operational overhead.